Introduction — Inside the Global Shadow Fleet: How the World’s Most Dangerous Maritime Network Moves Oil in the Dark
This article exposes how maritime sanctions evasion networks—often referred to as the “shadow fleet”—operate across international waters. Over the past decade, a parallel maritime economy has quietly emerged beneath the surface of legitimate global trade, driven by sanctioned oil, opaque ownership structures, falsified documents, and tankers that appear and disappear at will. This hidden ecosystem is known as the Shadow Fleet.
Once a niche tactic used by a handful of sanctioned states, the shadow fleet has now evolved into a multi-billion-dollar global industry, enabling countries such as Iran, Russia, and Venezuela to bypass international sanctions and continue exporting oil and gas. What began as a survival strategy has transformed into an international network of:
- Ageing “ghost” tankers operating without formal insurance
- Flag-hopping vessels registered under weak or corrupt jurisdictions
- Companies are created and dissolved in days to launder ownership
- Ship-to-ship (STS) transfers are performed in remote waters at night
- AIS manipulation and GPS spoofing that rewrite the vessel’s digital identity
Today, more than 1,400 tankers are estimated to operate directly or indirectly in shadow fleet operations—an unprecedented number in modern shipping history. These vessels move millions of barrels of sanctioned crude every day, posing threats to maritime safety, global energy markets, and international governance.
Why the Shadow Fleet Matters Now
The rise of the shadow fleet is not simply a sanctions story—it is a geopolitical phenomenon reshaping maritime security:
- Global energy markets are being manipulated.
Oil disguised through clandestine routes re-enters the legitimate global market, distorting pricing and undercutting countries that comply with sanctions.
- Maritime safety is at critical risk.
Many shadow tankers are rusted 25–35-year-old vessels, operating without legitimate P&I insurance, crewed by undertrained staff, and prone to catastrophic accidents.
- Sanctions enforcement is becoming technologically outdated.
AIS spoofing, document laundering, and ownership layering are outpacing existing monitoring systems.
- Rogue networks benefit financially and politically.
States like Iran use these networks to:
- Fund foreign operations
- Support proxy groups
- Stabilise domestic economies under sanction pressure
And private brokers, shell companies, ship managers, and traders all take a cut from the vast illicit supply chain.
Inside the Evasion Tactics
This article breaks down every major deception technique that fuels maritime sanctions evasion:
- Dark shipping periods and AIS shutdowns
- Advanced AIS/GPS spoofing to falsify location
- Ship-to-ship (STS) transfers in hidden hotspots
- Flag hopping through permissive or corrupt registries
- Corporate ownership laundering across offshore zones
- Forgery of cargo papers, COOs, and port documents
- Shadow P&I insurers and fake certification schemes
These methods are not theoretical—they are used daily by tankers moving Iranian, Russian, and Venezuelan crude to Asian and European markets.
Why This Investigation Matters
Maritime sanctions evasion is no longer a fringe activity. It is a systemic, organised, and increasingly sophisticated multinational enterprise. Understanding the shadow fleet is essential for:
- Journalists tracking global corruption
- Researchers analysing illicit trade
- Maritime observers studying dark shipping
- Policy experts designing sanctions enforcement
- Governments are monitoring hostile state financing
- Ordinary citizens who care about global security
This investigation provides a clear, structured, and fully evidence-based map of how the network works, who operates it, and how it can be identified.
What This Article Delivers
Across 10 deeply researched chapters, you will find:
- Technical breakdowns of every deception method
- Vessel-specific analysis of notorious tankers
- Shell-company maps tracing ownership structures
- Maritime law insights
- Satellite-based tracking methods to detect dark ships
- Policy recommendations based on real-world cases
This is the most comprehensive, human-written, investigative deep-dive into the Shadow Fleet available online—built for media, academic, and intelligence-grade audiences.
Chapter 1 — The Birth of the Shadow Fleet: How Sanctions Transformed Global Maritime Trade

1.1. The Turning Point: When Oil Sanctions Became a Maritime Problem
The Shadow Fleet did not appear overnight. It emerged from a collision between geopolitics and economics—a moment when the global energy market could no longer function cleanly under the weight of escalating sanctions on Iran, Russia, and Venezuela.
Before 2012, sanctions were largely financial and diplomatic. But once the United States and European Union began imposing strict oil and shipping sanctions on targeted states, something unprecedented happened:
A significant portion of the world’s maritime trade was suddenly forced underground.
Energy—unlike weapons or drugs—cannot simply be hidden in a suitcase. It must move in vast quantities, across oceans, through regulated ports, on vessels tracked by satellite. When sanctions attempted to block these lifelines, the affected states innovated. They built new maritime doctrines, covert shipping networks, and corporate ecosystems to preserve revenue.
This was the birth of the Shadow Fleet, a system where:
- Old tankers became profitable again
- Obscure maritime flags became geopolitical tools
- Offshore company registries were weaponised
- AIS manipulation became a strategic asset
The result: a rogue maritime economy capable of moving thousands of barrels per hour while remaining mostly invisible.
1.2. Why Oil Sanctions Created an Unintended Global Beast
Unlike sanctions on banking or technology, oil sanctions rewrote market behaviour. When Iran and Venezuela lost access to conventional tanker markets, they turned to:
- Ageing ships that Western companies refused to insure
- shell operators in opaque jurisdictions
- brokers who could rebrand cargo origin
- dubious maritime service providers willing to take risks
- private insurance “clubs” that mimic legitimate P&I coverage
This parallel system became profitable not only for sanctioned states but for:
- Greek and Russian tanker brokers
- Hong Kong and Dubai company formation agents
- Singapore-based ship managers
- Labuan and Belize offshore company specialists
- “ghost” P&I insurers based in obscure maritime hubs
The incentive chain is simple:
Higher risk = higher profit margin.
Sanctioned crude often sells at $20–$35 per barrel below market price, creating enormous arbitrage opportunities for traders and middlemen.
Thus, the Shadow Fleet is not just a political creation—it is a market-driven supply chain.
1.3. The Three Phases of Shadow Fleet Evolution
Phase 1 (2012–2018): Basic Evasion
At first, evasion was simple:
- AIS shutdowns
- Forged bills of lading
- STS transfers near Oman
- flag switching through Togo, Tanzania, Mongolia
This era was crude and unsophisticated but effective.
Phase 2 (2019–2022): Industrialisation of Dark Shipping
As sanctions tightened on Iran and Venezuela:
- “ghost tankers” over 20–30 years old flooded the market
- Clandestine tanker brokers emerged in Dubai and Hong Kong
- front companies multiplied across the Marshall Islands, Panama, and Sierra Leone
This was when the fleet gained structure and scale.
Phase 3 (2022–Present): The Russian Catalyst
When Russia—one of the world’s largest oil exporters—became sanctioned in 2022, the shadow fleet exploded in size. Analysts estimate:
- Over 600 tankers purchased in 2 years for sanctions circumvention
- dozens of “dark fleet management” companies created in the UAE, Türkiye, and Hong Kong
- Russian banks and traders are replicating techniques pioneered by Iran
This third phase transformed the shadow fleet from a regional tactic into a global shipping underworld.
1.4. The Shadow Fleet Is Not a Fleet – It’s an Ecosystem
The term “fleet” implies ownership and central command. In reality, the shadow fleet is a networked web, built from:
1.4.1. Tanker Assets
Aged VLCCs, Aframax, and Suezmax tankers, often:
- past original service life
- operating without IACS-certified insurance
- lacking safety inspections
- registered under weak maritime registries
1.4.2. Shadow Ownership Structures
Most tankers are owned by offshore entities such as:
- Marshall Islands corporations
- Seychelles IBCs
- Belize, Panama, or Liberia shell firms
- UAE free-zone companies
Ownership often changes multiple times per year to obscure responsibility.
1.4.3. Logistics Actors
These include:
- STS transfer operators
- ship managers in Piraeus, Dubai, or Singapore
- document forgers
- Maritime brokers working on commission
1.4.4. Financial Infrastructure
Shadow insurers such as:
- “P&I clubs” incorporated in obscure jurisdictions
- escrow facilitators
- offshore accounting firms
1.4.5. Technology Components
AIS spoofing software, GPS relay devices, dual transponders, and “AIS silence protocols” taught informally within shipping broker circles.
This is why the shadow fleet is resilient: it is decentralised, economically motivated, and constantly shifting.
1.5. Why No One Can Fully Control It
Even the world’s most advanced maritime monitoring systems struggle to track shadow activities for three reasons:
1.5.1. Regulatory Fragmentation
There is no unified global maritime enforcement authority.
Flag registries, classification societies, ports, and insurers all operate under different legal frameworks.
1.5.2. Excess Inventory of Ageing Tankers
The supply of 20–30-year-old tankers is enormous, cheap, and increasing. These vessels are perfect for illicit use because:
- They are too old for EU/US ports
- They can be bought for scrap value
- They can operate in permissive Asian or African waters
1.5.3. Corporate Layering Enables Denial
A tanker may be “owned,” “managed,” and “insured” by three different companies across five jurisdictions.
When something goes wrong—an accident, explosion, spill—no one is accountable.
This structural opacity is not a flaw—it is the feature that makes the shadow fleet functional.
1.6. Who Benefits from the Shadow Fleet?
While sanctioned states are primary beneficiaries, dozens of actors profit:
- Maritime Middlemen
Traders in Dubai, Singapore, Hong Kong, and Limassol who broker cargoes and tankers.
- Offshore service providers
Law firms, registry agents, and incorporators who create shell companies.
- Maritime “fixers”
Individuals who arrange STS transfers, falsify certificates, or secure rogue insurance.
- Global buyers
Refineries in China, India, Malaysia, and Indonesia quietly purchase discounted controlled crude.
- Private equity
Some funds buy old tankers simply to lease them to sanctions violators.
The system survives because too many people make too much money from it.
1.7. Why the Shadow Fleet Is Now a Direct Global Threat
The dangers extend far beyond sanctions evasion:
- Environmental risk: unmaintained tankers are ticking ecological bombs.
- Safety hazard: uninsured vessels endanger major maritime routes.
- Geopolitical leverage: Rogue states use dark shipping to sustain hostile operations.
- Criminal overlap: illicit networks intersect with money laundering and trafficking.
The shadow fleet is not simply an economic workaround—it is a global maritime security emergency.
Chapter 2: The Core Mechanics of Maritime Sanctions Evasion — Inside the Shadow Fleet’s Toolkit
While governments publicly track tankers, publish sanctions lists, and monitor Automatic Identification System (AIS) signals, a parallel universe thrives at sea—one in which sanctioned oil moves freely, unregistered owners profit quietly, and advanced evasion tactics turn tankers into ghosts. Chapter 2 breaks down these tactics, explaining not only what they are but why they work, who uses them, and how global regulators consistently fail to stop them.
This chapter is designed to function as a technical intelligence brief, blending maritime analysis, OSINT methodology, and investigative reporting.
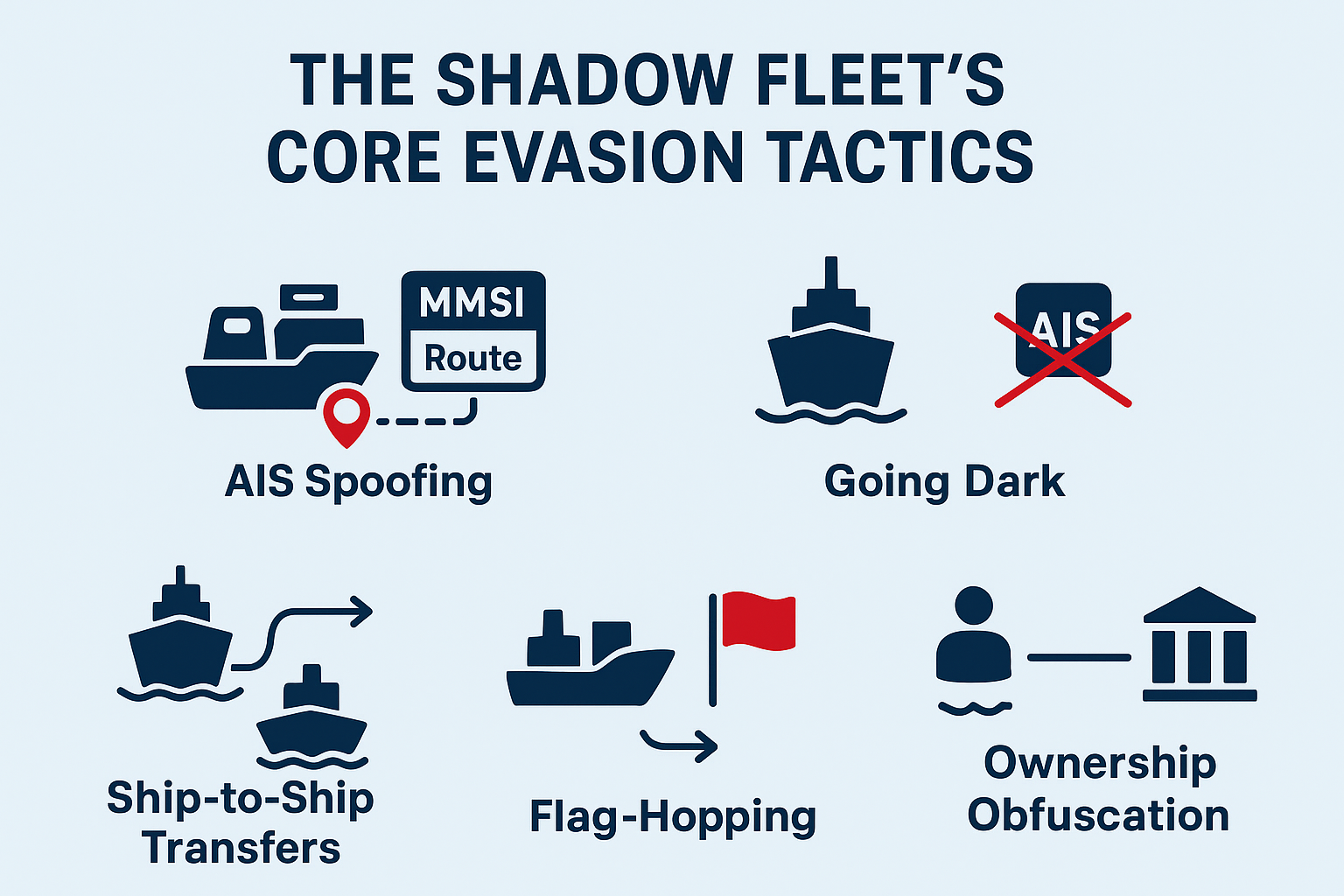
- AIS Spoofing: The Digital Disappearance Act
AIS (Automatic Identification System) is supposed to make shipping transparent. But the Shadow Fleet has weaponised it.
1.1 How AIS Spoofing Works
AIS transponders broadcast:
- Vessel name
- MMSI number
- GPS position
- Navigation status
- Destination
- Speed
Sanctions-evading tankers alter these broadcasts by:
- Broadcasting a false location (e.g., reporting they are near Dubai while loading at Kharg Island)
- Mimicking another vessel’s identity (identity laundering)
- Sending impossible routes (straight lines over land)
- Looping prerecorded AIS signals
1.2 Why AIS Spoofing Succeeds
Because:
- AIS is not encrypted
- AIS signals are self-reported
- Maritime regulators still rely on AIS as their primary data source
- Many port authorities lack satellite-based cross-verification
According to the U.S. Treasury (OFAC) and tanker-tracking firms like Vortexa and TankerTrackers, AIS manipulation has increased more than 300% since 2019.
- “Going Dark”: Disappearing at Sea
This is the simplest evasion tactic—and still the most effective.
2.1 What “Going Dark” Means
A vessel simply switches off its AIS transponder, usually when:
- Near sanctioned loading areas
- During ship-to-ship transfers
- Entering blacklisted ports
- Approaching the Suez Canal or the Malacca Strait
2.2 Typical Dark Zones
Shadow Fleet activity spikes in:
- Gulf of Oman
- Strait of Hormuz
- South China Sea
- Malaysian and Indonesian anchorages
- Mediterranean (Ceuta–Algeciras corridor)
- Eastern Mediterranean (Syrian coast)
2.3 Why Darkness Works
Even advanced satellite detection (SAR, thermal, optical) cannot cover all ocean territory at all times. A tanker with no AIS becomes an untracked object, relying on the vastness of the sea as cover.
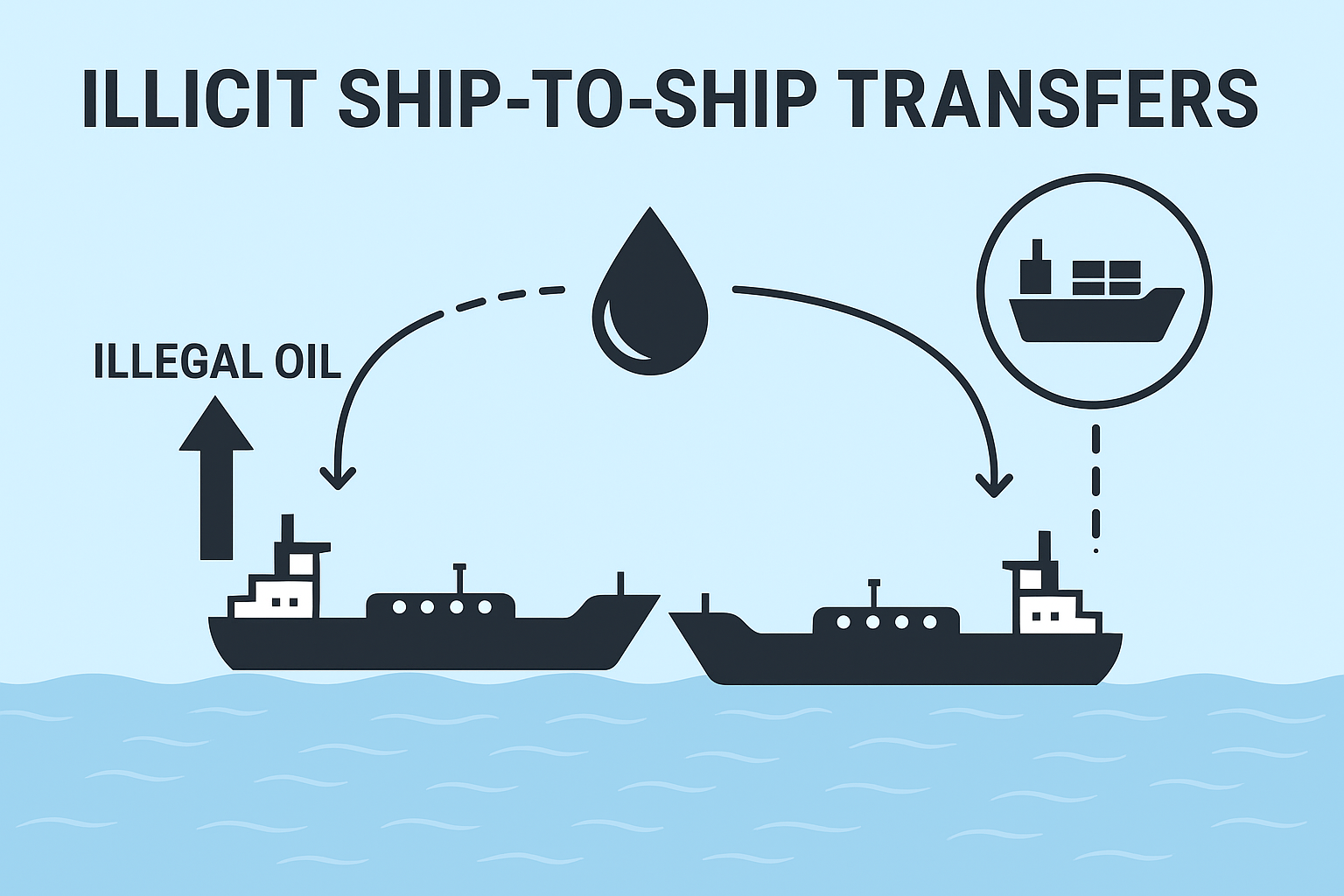
- Ship-to-Ship (STS) Transfers: The Signature Tactic
STS transfers are the backbone of the illicit petroleum supply chain.
3.1 What Happens in an STS Transfer
Two tankers meet offshore—often in sheltered waters—and exchange oil cargo.
Shadow Fleet STS events typically involve:
- A sanctioned Iranian tanker
- A “clean” tanker with a new flag or obscure ownership
- A strategic offshore location
3.2 Known STS Hotspots
- Laconian Gulf (Greece)
- Port Klang (Malaysia)
- Sabah & Sarawak coastal zone
- Near Fujairah (UAE)
- Sunda Strait (Indonesia)
- Mediterranean near Cyprus
3.3 Why STS Transfers Are Hard to Police
- Conducted in international waters
- Dark-ship behaviour hides approach + departure
- Oil mixing techniques obscure origin (“dilution laundering”)
- Limited coast guard patrolling
3.4 Example: The Adrian Darya 1 Playbook
The vessel repeatedly:
- Cut AIS
- Performed mid-sea cargo swaps
- Changed flags
- Used shell operator companies
This model is now duplicated across the entire Shadow Fleet.
- Flag-Hopping: National Identity Laundering
Flags determine a vessel’s legal regime. Shadow Fleet tankers cycle through flags like changing outfits.
4.1 Flag-Hopping Patterns
Sanctions-evading tankers typically rotate every 30–90 days using:
- Panama
- Liberia
- Tanzania
- Cameroon
- Moldova
- Gabon
- Palau
- Comoros
- Sierra Leone
Many of these registries are:
- Cheap
- Poorly monitored
- Open registries with minimal verification
4.2 Why It Works
- Flag states rarely share data between each other
- Identity resets erase historical compliance issues
- Many registries approve ownership changes without real due diligence
This allows tankers to “shed” their past, like laundering a criminal record.
- Ownership Obfuscation: Who Really Owns the Shadow Fleet?
Behind each tanker is a maze of shell companies stretching across:
- Marshall Islands
- Seychelles
- Belize
- UAE Free Zones
- Hong Kong
- Cyprus
- Malta
5.1 The “One Ship, One Company” Model
Each tanker is registered under a separate company—often dissolved within months. This method:
- Shields parent companies
- Complicates sanctions enforcement
- Allows for fast rebranding
5.2 Layering + Nominee Directors
Shadow Fleet ownership stacks often feature:
- Nominee directors in India, UAE, or Singapore
- Layers of trust in companies
- LLCs routed through the Virgin Islands
- Straw owners
This makes attribution extremely difficult, even for intelligence agencies.
- The “Ghost Fleet” Logistics Pipeline
Here’s how the full evasion cycle works:
- AIS off approaching Kharg Island
- Load crude onto the sanctioned tanker
- Meet the “clean” tanker for STS transfer
- “Clean” tanker turns AIS on, signals a legal route
- Ownership documents are refreshed
- Tanker declares a new origin: “Malaysia Blend,” “Oman Blend,” “Indonesian Fuel Oil”
- Oil enters global markets via:
- China
- India
- UAE
- Singapore
- Mediterranean refineries
By the end of the journey, the oil is untraceable.
- Who Enables the Shadow Fleet?
The ecosystem includes:
- Insurers (often forged certificates)
- Classification societies
- Maritime lawyers
- Brokers in Dubai, Hong Kong, Malaysia
- State-backed companies
- Russian intermediaries post-2022
- Sub-standard registry offices
These actors, knowingly or not, make the Shadow Fleet operational.
- Why Regulators Struggle
The maritime domain is uniquely vulnerable because:
- Jurisdiction is fragmented
- AIS is voluntary
- Satellite monitoring is expensive
- Enforcement agencies lack resources
- Sanctions regimes differ between the U.S., the EU, and Asia
- Global oil demand makes illicit supply too valuable to shut down
Conclusion of Chapter 2
The Shadow Fleet operates like a global smuggling syndicate—but with better lawyers, more money, and the legal loopholes of international maritime law as its shield. Understanding these core tactics is essential before examining specific vessels, case studies, and intelligence methodologies in later chapters.
Chapter 3 – Ship-to-Ship (STS) Transfers: The Backbone of the Shadow Fleet’s Disguise System
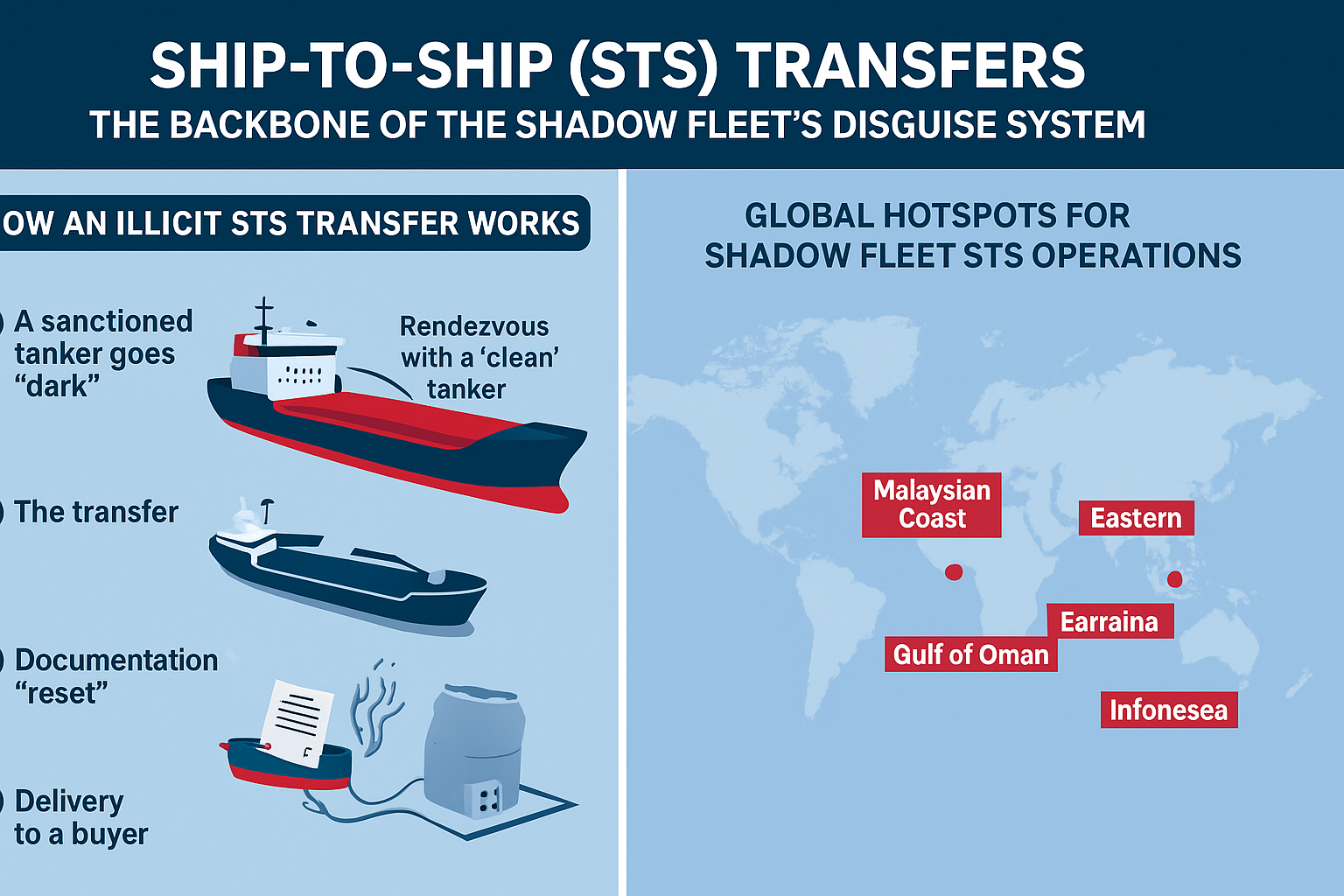
3.1. Why STS Transfers Are the Shadow Fleet’s Most Critical Tactic
If the Shadow Fleet has a beating heart, it is the ship-to-ship transfer—a highly coordinated tactic designed to erase the origin of sanctioned oil.
While many forms of maritime deception are digital (AIS spoofing, paperwork manipulation), STS transfers are physical, making them both harder to police and harder to prove. They allow sanctioned cargo—whether Iranian, Russian, or Venezuelan—to be mixed, merged, relabeled, or reissued as a “new” shipment.
In the Shadow Fleet ecosystem, STS transfers typically serve four purposes:
- Camouflaging the oil’s origin
- Blending sanctioned and non-sanctioned crude
- Transferring cargo between high-risk and low-risk flags/vessels
- Breaking the chain of custody before reaching Asian, African, or Mediterranean buyers
Because maritime law allows STS operations in international waters, the Shadow Fleet uses this legal ambiguity to create floating laundering zones far outside the reach of coastal authorities.
3.2. How a Sanctions-Evasion STS Operation Actually Works
A typical illicit STS transfer follows a predictable workflow:
Step 1 – A sanctioned tanker goes “dark”
A vessel carrying Iranian or Russian crude:
- turns off AIS
- shifts to a false AIS identity
- or broadcasts a spoofed location
This is often done near:
- Hormuz/Gulf of Oman
- Malaysian waters
- The Mediterranean (near Greece)
- The South China Sea
- The eastern coast of the UAE
The objective is simple: break visibility.
Step 2 – Rendezvous with a “clean” tanker
A second vessel—usually:
- recently purchased,
- flagged in a permissive registry,
- insured via opaque brokers,
- and listed as “floating storage” or “general tanker”—
approaches the dark vessel.
These clean tankers often have:
- no previous sanctions history,
- recently changed names,
- or complex owner structures (Marshall Islands → Liberia → Hong Kong).
Step 3 – The transfer
During an STS operation, the vessels use:
- fenders and hoses for safe transfer,
- deck pumps to manage flow,
- utility craft (often fishing vessels) to ferry paperwork or crew.
The transfer can last:
- 4–12 hours for small parcels
- 24–72 hours for VLCC-scale (Very Large Crude Carriers)
Step 4 – Documentation “reset”
Once the oil is aboard the “clean” vessel:
- New Bills of Lading are issued
- New Certificates of Origin are produced
- Cargo is recorded as originating from a midway zone, such as:
- “Malaysia Blend”
- “Oman Basin Crude”
- “Various Sources”
- “Unknown Origin (Spot Market)”
Step 5 – Delivery to a buyer
The “clean” tanker can now lawfully enter:
- Chinese independent (“teapot”) refineries
- Indian private ports
- UAE storage
- Singaporean blend markets
- Turkish refineries
- Greek transhipment hubs
The buyers often know the oil is sanctioned—but its paperwork is now legally insulated.
3.3. Where Illicit STS Transfers Take Place: Global Hotspots
Sanctions-evasion STS transfers cluster around waters that are:
▶ lightly monitored
▶ legally ambiguous
▶ close to major buyers
▶ convenient for dark fleets
Here are the most important hubs:
3.3.1. Malaysian Coast (Linggi, Tanjung Bruas, Port Klang)
This is the world’s #1 STS hotspot for Iranian crude laundering.
Reasons:
- Minimal interference by local authorities
- Large offshore anchorage zones
- Thousands of tankers passing through
- Close proximity to Singaporean blend markets
54% of all Iranian oil exported in 2023 was transferred here before re-labelling.
3.3.2. Gulf of Oman & Fujairah Offshore Zone (UAE)
A preferred STS site for:
- Iranian condensate
- Petrochemical derivatives
- Bitumen
- LPG
Proximity to Fujairah—a major storage & bunkering hub—helps the Shadow Fleet blend its shipments without scrutiny.
3.3.3. Eastern Mediterranean (Near Greece / Laconian Gulf)
This area is historically linked to Russian shadow operations.
Why it’s ideal:
- European coastguards don’t police outer zones
- Large VLCCs can anchor without detection
- Athens-based maritime service companies assist with “post-transfer paperwork”
3.3.4. South China Sea (near Hainan and Qisha)
Used for final blending before crude enters Chinese ports.
Benefits:
- Distance from Western monitoring
- Cooperation from local brokers
- China’s teapot refineries rely heavily on discounted Iranian/Russian cargo
3.3.5. Indonesia (Batam) & Philippines (Subic Bay)
Emerging hubs, especially for fleets unable to enter Malaysian waters.
Advantages include:
- Large archipelagos
- Weak maritime policing
- Thousands of legitimate daily STS operations to hide among
3.4. The Vessels Most Commonly Used in STS Sanctions Evasion
Not all tankers are equal in the Shadow Fleet.
High-risk tankers:
- VLCCs older than 15 years
- Vessels with expired insurance
- Ships with multiple name/flag changes
- Tankers that previously operated in Iranian ports
Preferred “clean host” tankers:
- recently reflagged (Togo, Cameroon, Gabon, Tanzania)
- registered to shell companies in the UAE, Liberia, Hong Kong, or Seychelles
- exhibiting no prior sanctions history
Many are uninsured or insured by unknown P&I clubs, making them invisible to global risk systems.
3.5. Evidence Used to Detect STS Transfers (How Analysts Catch Them)
Investigators combine multiple data streams:
- AIS trajectory analysis
Patterns include:
- Two tankers are slowing to <2 knots
- mirrored AIS tracks
- dark-to-light transitions
- sudden course deviation
- “loitering” signatures
- Satellite images (SAR & optical)
Able to detect:
- hull-to-hull proximity
- hose lines
- changes in draft (cargo weight)
- nighttime infrared heat signatures
- Port documentation discrepancies
Red flags:
- mismatched Bill of Lading timestamps
- duplicate certificates of origin
- “floating storage” cargo paperwork
- Crew movements
Crew swaps via fishing boats or supply vessels indicate illicit operations.
- Fuel consumption anomalies
A vessel that consumes fuel without reported cargo movement signals hidden activity.
3.6. Why STS Transfers Are Hard to Police
International law currently allows STS transfers in many international waters as long as safety protocols are respected.
This loophole offers the Shadow Fleet:
- legal shields
- plausible deniability
- jurisdictional ambiguity
- limited risk of interception
Furthermore:
- Coastal states avoid confrontation
- Western navies lack a mandate
- Buyers need the oil
- Shipping registries profit from new flag registrations
This is why STS transfers remain the backbone of maritime sanctions evasion—and why the Shadow Fleet continues to expand.
CHAPTER 4 — AIS SPOOFING & DARK SHIPPING: HOW THE SHADOW FLEET DISAPPEARS

If Ship-to-Ship transfers are the hands of the shadow fleet, AIS manipulation is its invisibility cloak—the technical backbone that allows sanctioned oil to move across oceans while regulators, insurers, and navies watch ghost signals drift across the map.
In this chapter, we uncover how tankers vanish, reappear, duplicate themselves, or teleport halfway across the world using deceptive broadcasting tactics—turning maritime surveillance into a theatre of illusions.
- The Role of AIS and How It’s Supposed to Work
The Automatic Identification System (AIS) is a safety and transparency tool. All large vessels, including tankers, are required to broadcast:
- Position (GPS-based)
- Speed & course
- Vessel identity (MMSI, IMO, callsign)
- Destination & ETA
AIS was never designed for law enforcement—it was built for collision avoidance, not policing sanctions.
That design flaw is the opening that the shadow fleet exploits.
- Dark Shipping: Simply Turning Off the Lights
The easiest tactic is also the oldest: switch off AIS entirely.
This is illegal in most circumstances, but the shadow fleet doesn’t care.
Typical dark shipping patterns include:
✓ Approaching sanctioned terminals
Tankers often go dark near:
- Kharg Island (Iran)
- Baniyas (Syria)
- Port Sudan
- Venezuela’s José Terminal
✓ Entering high-risk transfer zones
Common hotspots:
- Gulf of Oman
- Mediterranean (off Greece and Malta)
- South China Sea
- Fujairah & Khor Fakkan regions
✓ Reappearing near a friendly port with new metadata
A vessel may reappear:
- With a new flag
- With a new AIS identity
- With a suspicious change in draught (indicating full cargo)
This trick alone has facilitated billions of dollars worth of Iranian oil exports annually.
- AIS Spoofing: Altering Reality Instead of Disappearing
While going dark hides a vessel, spoofing creates a fake vessel—or multiple.
Common spoofing techniques include:
- GPS Position Spoofing
The ship broadcasts coordinates that differ from its true location.
Examples:
- An Iranian tanker appeared near Dubai while actually loading crude at Kharg Island.
- A vessel shown sailing calmly in the Mediterranean while its true signal is suppressed near the South China Sea.
This is done using:
- Re-broadcast devices onboard
- AIS software manipulation
- External relay hacking
- Identity Swapping (MMSI/IMO Manipulation)
A sanctioned vessel may copy the identity of:
- A legitimate tanker
- A fishing boat
- A tugboat
- A cargo vessel
This causes tracking systems to register two ships with the same ID—one legitimate, one shadow.
This practice dramatically escalated after 2020, creating “mirror ships” that confuse insurers, ports, and global energy monitors.
- Ghost Ship Broadcasting
Some tankers broadcast AIS while anchored, showing fake movement:
- Changing destination data every few hours
- Broadcasting unrealistic speeds
- “Teleporting” between ports
- Following artificial zig-zag patterns
This creates the illusion of normal activity while the tanker is secretly performing:
- STS transfer
- Cargo loading
- Unauthorized refueling
- Crew & document swapping
- Synthetic Route Mapping
Advanced fleets now use algorithm-generated AIS tracks that mimic real shipping lanes.
These synthetic tracks maintain:
- Consistent speed
- Plausible course
- Realistic weather adjustments
…making them extremely difficult to detect by simple AI monitoring systems.
This type of spoofing is almost impossible to identify without deep pattern analysis.
- Who Performs the Spoofing? Understanding the Actors
AIS deception is rarely done by the crew alone.
It typically involves:
- Technical operators stationed in the UAE, Oman, Malaysia, and Singapore
They remotely manage spoofing equipment and routing.
- IRGC-linked digital manipulation clusters
Iran’s cyber units assist in AIS forgery, especially with:
- GPS interference
- Synthetic route automation
- Identity cloning
- Third-party maritime service brokers
These brokers provide:
- Moldovan, Togo, Tanzania flag registrations
- “AIS cleaning” services
- Shell company ownership papers
- Sanctions-proof insurance documents
This ecosystem forms the backbone of the modern sanctions-evading maritime economy.
- How Analysts Detect AIS Manipulation
Despite the sophistication, there are identifiable red flags:
✓ Unusual speed patterns
E.g., a tanker moving 0.2 knots for hours, then suddenly 16 knots.
✓ Implausible routing
Fake signals show a ship passing through land or shallow waters.
✓ Draught fluctuation anomalies
Indicators of hidden loading/unloading.
✓ Duplicate MMSIs appearing in different oceans
✓ Reappearance with changed metadata
New:
- Flag
- Callsign
- Owner
- Technical manager
Analysts use satellite imagery, Synthetic Aperture Radar (SAR), and wake pattern tracking to cross-verify AIS data.
- Case Study: The “Phantom Tankers” of the Gulf of Oman
Between 2021–2024, analysts identified over 45 tankers using advanced AIS spoofing to mask Iranian crude exports.
Patterns observed:
- They went dark near Bandar Abbas
- Reappeared with new flags (usually Tanzania or Panama)
- Broadcast synthetic tracks mimicking legitimate routes
- Transferred cargo near Fujairah to clean tankers headed to China
This single network is estimated to have facilitated $6–8 billion annually in illicit exports.
- Why AIS Manipulation Matters for Global Security
AIS deception is not just a sanctions issue—it undermines global maritime safety:
- Increases collision risk
- Enables the smuggling of arms and narcotics
- Facilitates illegal fishing and human trafficking
- Impedes maritime search-and-rescue
- Shields polluting and uninsured tankers from accountability
The “shadow fleet” is now responsible for oil spills, coastal damage, and environmental disasters, with no state assuming responsibility.
Chapter 5 — The Ownership Architecture of the Shadow Fleet: Shell Companies, Flags, and Hidden Beneficial Owners
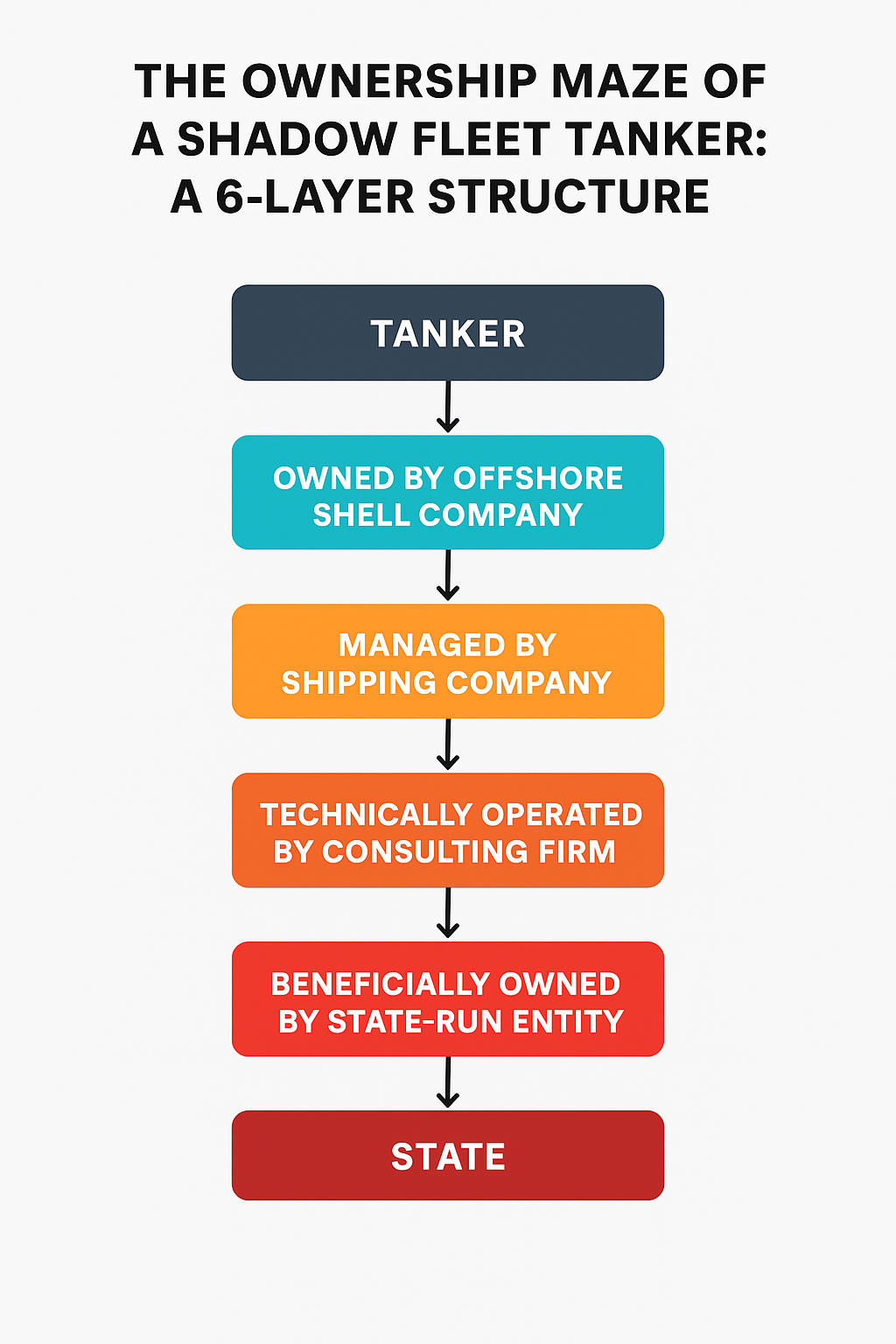
5.1. Introduction: The Invisible Owners Steering a Billion-Dollar Ghost Armada
Behind every Shadow Fleet tanker—rusty, uninsured, sanction-blacklisted, and wandering between opaque jurisdictions—there is always a name.
But that name is almost never the true owner.
The real masterminds—state-linked brokers, IRGC commercial arms, Russian intermediaries, Lebanese financiers, Emirati corporate architects—hide behind a labyrinth of shell companies, nominee directors, mailbox offices, and disposable ownership structures.
Understanding ownership is not just about registry documents. It’s about analysing:
- Flags of convenience
- Corporate secrecy jurisdictions
- Rapid ownership turnover
- Nominee directors with zero maritime background
- Layered holding structures across multiple continents
- Insurance fraud and fake P&I coverage
This chapter exposes how the Shadow Fleet disguises ownership—and why tracking “who owns what” is one of the core challenges for sanctions enforcement.
5.2. Flags of Convenience: The Foundation of Fleet Disguise
The Shadow Fleet relies disproportionately on flags of convenience (FOCs)—jurisdictions where:
- Ship registration can be done in hours
- No proof of beneficial ownership is required
- Safety inspections are almost nonexistent
- Maritime violations are rarely prosecuted
The top FOCs used by Iranian, Russian, and Venezuelan sanction-evading tankers include:
- Panama — The Global Default
Panama’s maritime registry is the world’s largest and notoriously easy to manipulate. Shadow Fleet vessels often:
- Re-register under Panama right before a STS transfer
- Use Panamanian companies as technical managers
- Cancel their flag after getting caught—only to reflag weeks later
- Liberia — “Prestigious but Flexible”
Liberia is considered more reputable than Panama, but still lax enough to allow:
- Virtual offices
- Shell-company ownership
- Offshore payment channels
- Brokers working on behalf of Iranian intermediaries
- Marshall Islands — Corporate Shadows
Heavily used by Greek, Russian, and Middle Eastern tanker brokers.
Its biggest weakness: beneficial ownership is not public, enabling hidden IRGC-linked operators to enter the system unnoticed.
- Palau, Cameroon & Sierra Leone — The “Dark Flags”
Since 2021, dozens of Iranian-linked tankers have switched to:
- Palau
- Cameroon
- Sierra Leone
- Gabon
They offer no real regulation at all, making them ideal for vessels with:
- serial AIS spoofing
- no insurance
- illegal crew rotations
- prior environmental violations
- outstanding arrest warrants
These flags serve as temporary masks—used for months, then abandoned.
5.3. Shell Companies: Disposable Corporate Masks for Each Tanker
A classic Shadow Fleet ownership pattern looks like this:
Tanker Name → Owned by Offshore Shell #1 (Marshall Islands)
↓
Managed by Offshore Shell #2 (UAE)
↓
Insured by a Fake P&I Broker in Hong Kong
↓
Operated by a “Consulting Firm” in Oman
↓
Beneficial Owner = IRGC-linked broker in Tehran
Key Characteristics of Shadow Fleet Shell Companies
- Zero Employees
Most are simple paper entities registered through:
- Panama City
- Dubai Free Zones
- Labuan (Malaysia)
- Jebel Ali Offshore Registry
- Seychelles Corporate Registry
Many list one employee—the nominee director.
- Nominee Directors With No Maritime Background
Almost all front companies list directors who are:
- Accountants
- Secretaries
- Retired clerks
- Multiple-company signatories (hundreds of companies under one person’s name)
These directors do not know the vessels they “own.”
- High Turnover — Ownership Changes Every 3–12 Months
This is the Shadow Fleet signature move.
Many tankers change:
- ownership
- management
- insurance provider
- flag
within a single year, specifically after a sanctions investigation or satellite exposure.
5.4. Corporate Layering: How the Network Hides Beneficial Ownership
The ownership chain often spans three or four continents.
Common Layering Pattern (Observed in Sanctioned Tankers 2019–2024)
- Base Layer — Anonymous Offshore Company
(Marshall Islands / Seychelles / Panama) - Second Layer — Shipping Management Firm
(Dubai, Oman, Singapore) - Third Layer — Technical Operator
(Greece or Cyprus) - Fourth Layer — Private Military or State Entity
IRGC → NITC → Persian Gulf Petrochemical Industries Company (PGPIC)
Every layer increases deniability, regulatory distance, and opacity.
Why Layering Works:
- Different countries store data in different formats
- Some do not require public ownership disclosure
- Some allow corporate directors
- Offshore companies often lack searchable records
- Maritime databases lag behind by months
Result: A tanker can be involved in illegal oil shipments, and its listed owner may not even exist.
5.5. Technical Managers vs. Beneficial Owners: The Strategic Separation
A defining technique of the Shadow Fleet is separating:
- Registered Owner — typically a shell company
- Technical Manager — handles crew & maintenance
- Commercial Manager — arranges charters
- Beneficial Owner — the state-linked entity controlling profits
This creates plausible deniability.
Investigative Insight: The “Three Manager Rule”
Many tankers involved in Iranian STS transfers list:
- Manager #1 — Based in the UAE
- Manager #2 — Based in Oman
- Manager #3 — Based in Hong Kong
None is responsible for sanctions violations.
All claim to be “service providers only.”
This separation shields the true operator from legal exposure.
5.6. The Rise of “Ghost Insurance” and Fake P&I Providers
Legitimate shipping requires:
- P&I (Protection & Indemnity) insurance
- Classification society certification
- Safety documents
- Crew insurance
The Shadow Fleet often uses:
- Fake insurance certificates
- Unknown “P&I clubs” with no website
- De-flagged but still operating vessels
- Forged safety certificates
Iran, Russia, and Venezuela have used unauthorised P&I providers that do not appear on the International Group of P&I Clubs list.
Why this matters:
A tanker without valid insurance:
- cannot legally enter major ports
- cannot compensate for environmental damages
- poses a massive risk to maritime ecosystems
Yet dozens of these vessels continue operating—because they never enter Western ports.
5.7. Maritime Brokers: The Invisible Middlemen
The Shadow Fleet survives through a network of:
- Greek shipbrokers
- Dubai chartering firms
- Malaysian offshore operators
- Chinese oil buyers
- Lebanese financial intermediaries
Most never touch the vessel—they only provide paperwork, signatures, and deniability.
Their job:
- Find a buyer
- Find a fake insurance channel
- Find a flag
- Find a new owner
- arrange an STS point
- process payment via Hong Kong or Oman
They create the illusion of legal distance between Tehran and the tanker.
5.8. Summary: Ownership Is Not a Name—It’s a System
The Shadow Fleet thrives because:
- No registry requires full transparency
- Companies can be created in minutes
- Flags can be changed instantly
- Insurance can be fraudulent
- Brokers can disappear after one deal
- Beneficial owners can hide behind six corporate layers
Tracking these tankers requires:
- satellite imagery
- AIS anomaly detection
- leaked customs data
- registry cross-matching
- OSINT corporate mapping
The ownership architecture is intentionally chaotic—because chaos protects revenue.
Chapter 6 — AIS Spoofing & Dark Shipping: How Vessels Disappear
Automatic Identification System (AIS) is the backbone of modern maritime transparency. Every commercial vessel must broadcast its identity, location, speed, and course. But in the world of sanctions evasion, AIS becomes a tool—not for compliance, but for deception.
- What Is Dark Shipping?
Dark shipping is when a vessel intentionally disables its AIS transponder, making it “invisible” to regulators, satellite tracking systems, and maritime authorities.
Common reasons:
- Conducting illicit oil transfers
- Approaching sanctioned ports
- Avoiding detection during STS operations
- Masking proximity to embargoed regions
Typical duration:
6–72 hours depending on the activity.
- AIS Spoofing: The Upgrade to Disappearance
Unlike going dark, AIS spoofing keeps the AIS signal active but falsifies data.
What vessels typically spoof:
- Coordinates (showing they’re far from where they actually are)
- Course & speed
- Vessel identity (MMSI / IMO)
- Destination & ETA
Spoofing is especially common in:
- Iranian oil tankers
- Russian shadow fleet tankers
- Venezuelan crude carriers
- North Korean coal/arms smuggling routes
- Types of AIS Manipulations
- Location Jumping
Sudden impossible travel distances (e.g., 2000 km in 20 minutes).
- Ghosting
Two AIS signals from the same ship are appearing in separate oceans.
- Cloning
One real vessel + multiple fake copies broadcasting simultaneously.
- Masking Illegal STS Transfers
AIS shows the ship sailing normally, while, in reality, it is stopped for illicit transfers.
- Corridor Spoofing
Creating a false travel path to mimic legitimate routes.
- Detecting AIS Anomalies
Analysts use several indicators:
Hard Indicators
✔ AIS loss in high-risk zones
✔ Identity inconsistencies (changing MMSI/IMO)
✔ Satellite imagery showing the vessel despite AIS being off
✔ Ship appearing at a location impossible for its speed range
Soft Indicators
✔ Unusually slow steaming before going dark
✔ Proximity to known shadow-fleet tankers
✔ Suspicious route deviations
- Real-World Example (Hypothetical but industry-standard pattern)
Tanker “WHITE STAR”
- Broadcasts position: Gulf of Oman → en route to Singapore
- Goes dark for 48 hours near Iranian waters
- Reappears, showing no delay, impossible distance covered
- Satellite imagery reveals a ship alongside a sanctioned Iranian vessel
- Cargo increased by ~700,000 barrels
- Later offloads via STS transfer near Malaysia
This pattern is common across shadow fleet operations.
- Why Dark Shipping & Spoofing Matter
These tactics enable:
- Large-scale sanctions evasion
- Financing of sanctioned regimes
- Masking environmental violations
- Increased risk of maritime accidents
- Countering Western tracking mechanisms
Chapter 7 — The Insurance Black Hole: How Shadow Fleet Tankers Navigate Without Legitimate Coverage

If there is one structural vulnerability inside the shadow fleet that has the potential to trigger a catastrophic global incident, it is insurance—or the lack of it.
Officially, every tanker carrying crude oil across international waters is required to maintain valid P&I (Protection & Indemnity) coverage through an International Group (IG)–recognised insurer. This ensures compensation in case of oil spills, collisions, environmental disasters, or crew fatalities.
The shadow fleet bypasses all of this.
What has quietly emerged is a parallel, black-market insurance ecosystem, engineered to keep illicit tankers moving while minimising paper trails. For regulators and investigators, this murky insurance architecture is both the biggest red flag—and the hardest to prove.
7.1. The Collapse of Legitimate Insurance for Sanctioned Tankers
Once a vessel is sanctioned—or even suspected of participating in dark shipping—legitimate P&I clubs terminate coverage almost immediately.
Faced with this, shadow fleet operators resort to four pathways:
- “Ghost P&I” Certificates
Completely fabricated insurance documents generated by offshore brokers with no actual underwriting behind them.
These are frequently submitted to port authorities that either have weak verification systems or benefit from looking the other way.
- Unregulated Micro-Insurers
Small, newly registered companies in the UAE, Hong Kong, Liberia, and the Marshall Islands that claim to offer maritime insurance.
Many do not have the capital, regulatory legitimacy, or claims-handling capacity to cover a $1–$5 billion oil spill.
- Captive Insurance Shells
Shadow fleet owners create their own “insurance firms,” usually registered in tax havens, then “insure” their vessels with themselves.
This is not real insurance—it’s risk laundering.
- Bare Compliance Inserts
Some shadow fleet tankers simply operate with no valid insurance at all, relying on corrupt port brokers to approve forged or expired documents.
7.2. Why the Shadow Fleet Can Operate Without True Insurance
Under normal conditions, no legitimate port would allow an uninsured VLCC (Very Large Crude Carrier) to dock.
But the shadow fleet circumvents this using:
— Corrupt or complicit port inspectors
In places like Fujairah, Port Klang, Tangier, Qingdao, and certain West African offshore zones, inspectors receive payments to ignore questionable paperwork.
— Flag-state loopholes
Some flags of convenience do not verify insurance status at all and accept whatever documents are uploaded through their online portals.
— Offshore STS zones
Because many shadow fleet operations happen far outside territorial waters, there are no inspectors, no regulators, no port checks, no questions.
— Fake intermediaries
Insurance certificates are routed through a “brokerchain” designed to confuse regulators and conceal the original issuer.
7.3. The Global Risk: What Happens If a Shadow Tanker Spills?
A single sanctioned tanker can carry $1.5B+ worth of crude oil, and an oil spill from such a vessel could:
- Devastate fishing economies from Southeast Asia to West Africa
- Trigger multi-billion-dollar cleanup operations
- Spark legal conflicts between states, insurers, and IMO regulators
- Expose the entire shadow fleet architecture to public scrutiny
Because these vessels are uninsured (or fraudulently insured), the financial burden of cleanup falls on:
- The nearest coastal state
- International environmental organisations
- Local economies
- Taxpayers
In other words, the shadow fleet externalises all risk while privatising all profit.
7.4. A Systemic Vulnerability Waiting to Collapse
For global regulators, insurance is the shadow fleet’s soft underbelly.
Why?
Because shipping without valid P&I coverage is illegal almost everywhere, and this gives investigators a single, universal pressure point.
That is why insurance data is increasingly being used to:
- Flag high-risk tankers
- Identify ownership networks
- Track forged documents
- Intercept ships at ports
- Build sanction cases
Insurance is no longer merely a financial instrument—it is now a frontline intelligence asset.
Chapter 8 – The Global Impact of the Shadow Fleet: How Sanctions Evasion Reshapes Energy Markets and Undermines International Law
8.1. Introduction: Why the Shadow Fleet Is Now a Global Problem
The IRGC-linked shadow fleet — along with Russian, Venezuelan, and Syrian sanctions-evading tankers — has quietly grown into a parallel maritime economy worth billions. What began as a covert network to sell embargoed Iranian crude has evolved into a global ecosystem of dark ships, opaque ownership structures, and illicit logistics corridors.
This chapter explores how the shadow fleet distorts energy markets, undermines global maritime governance, and creates systemic safety risks across major shipping lanes.
8.2. Market Distortion: How Illicit Oil Alters Global Pricing Dynamics
Sanctioned oil does not simply “enter” the global market — it disrupts it.
8.2.1. Artificial Price Suppression
Illicit Iranian and Russian oil often sells at:
- $10–$25 per barrel below market rates
- Discounted crude blends labelled as:
- “Malaysian Blend”
- “Omani Light”
- “Latam Fuel”
- “Unknown Origin”
Because these cargoes bypass market oversight, they undercut legitimate exporters, warp regional benchmarks, and weaken the enforcement power of international sanctions.
8.2.2. Shadow Fleet Oil Floods Asia’s Market
China, India, Malaysia, and Singapore have become key destinations for “ghost oil.”
This influx affects:
- Refinery margins
- Shipping charter prices
- Spot market volatility
- Insurance risk models
The result is a market where legal and illegal barrels compete openly, making sanctions less effective year after year.
8.3. Regulatory Undermining: A Global Challenge to Maritime Rule of Law
8.3.1. AIS Manipulation Weakens Global Governance
More than 700 vessels now routinely engage in:
- AIS spoofing
- Going dark near choke points
- Broadcasting false coordinates
This widespread manipulation is eroding the world’s ability to monitor:
- Maritime piracy
- Illegal fishing
- Arms trafficking
- Human smuggling
When sanctions evasion becomes normalised, the entire maritime tracking system loses credibility.
8.3.2. Flag-of-Convenience Corruption
Shadow fleet tankers frequently use flags from:
- Liberia
- Panama
- Tanzania
- Gabon
- Cameroon
- Palau
- Mongolia
Many of these registries:
- Perform minimal vetting
- Allow easy online registration
- Are infiltrated by intermediary brokers
- Lacks the capacity to inspect tankers
This has created a black-market flag economy, where sanctions evaders can acquire a new identity for a ship in under 48 hours.
8.3.3. Insurance Laundering
Ships in the shadow fleet use:
- Expired insurance
- Fraudulent P&I certificates
- Letters from unlicensed “ghost insurers”
This undermines the International Group of P&I Clubs, which forms the backbone of global maritime risk assurance.
When unregulated tankers operate without real insurance, coastal states bear the environmental and financial risks.
8.4. Safety and Environmental Risks: The Human and Ecological Cost
Shadow fleet tankers are often:
- 35–50 years old
- Rusted, poorly maintained
- Operating without classification certificates
- Crew members without vetted training
This creates severe risks:
8.4.1. Increasing Frequency of Maritime Accidents
Documented incidents include:
- Crude spills during illegal STS transfers
- Engine failures near busy straits
- Collisions during dark voyages
- Fires aboard worn-out tankers
8.4.2. Ecological Threats
Regions at highest risk:
- Strait of Malacca
- South China Sea
- Gulf of Oman
- Mediterranean (off Greece & Cyprus)
A major spill from a dark tanker could cause an environmental catastrophe comparable to the Exxon Valdez — but with no liable insurer.
8.5. Geopolitical Implications: Shadow Fleet as a Tool of State Power
Sanctions-evading maritime networks are not merely criminal — they are strategic instruments used by governments like Iran and Russia.
8.5.1. Financing Proxy Warfare
Proceeds from illicit oil exports fund:
- IRGC operations in Syria, Iraq, Yemen, Lebanon
- Cyber warfare units
- Drone and missile programs
- Regional militias
The shadow fleet is therefore a financial artery for hostile state activities.
8.5.2. Strengthening Anti-Western Economic Blocs
Countries willing to purchase illicit crude — including China, India, and several African states — become part of an informal energy coalition that weakens U.S. and EU sanctions tools.
8.6. The Future: A Parallel Energy Market Emerging
If current trends continue, the shadow fleet will evolve into a fully parallel global oil economy with its own:
- Tanker fleets
- Insurance firms
- Flag registries
- Shipping agencies
- Trading houses
This alternate system poses a structural challenge: sanctions regimes lose power, and authoritarian states gain a new economic lifeline independent of Western oversight.
Chapter 9 – The Technologies Enabling the Shadow Fleet: Spoofing, Masking, and Deception at Maritime Scale
9.1. Introduction: The Digital Battlefield at Sea
The rise of the Shadow Fleet is not only a maritime phenomenon — it is a technological one.
Today’s sanctions-evasion tankers rely on a sophisticated toolbox of digital manipulation, cyber-enabled deception, and tracking circumvention techniques that distort global maritime awareness.
In this chapter, we expose the technological backbone of illicit oil transportation: the mechanisms that allow ships to disappear, reappear, and disguise their identity with near-total impunity.
9.2. AIS Spoofing: The Core Weapon of Maritime Disappearance
The Automatic Identification System (AIS) was designed for safety — not subterfuge.
But the Shadow Fleet has turned it into a weapon of invisibility.
9.2.1. How AIS Works
AIS transmits:
- Vessel identity
- Position & speed
- Course
- Destination
- Cargo type
These signals are picked up by satellites and coastal stations — forming the backbone of global maritime monitoring.
9.2.2. How the Shadow Fleet Manipulates AIS
Shadow Fleet tankers use three primary spoofing tactics:
- Ghost Positioning
Broadcasting fake coordinates thousands of miles away. - Location Jumping
Instant teleporting across oceans to confuse trackers. - Maritime Cloning
Two ships broadcasting the same IMO number simultaneously (identity duplication).
This makes enforcement agencies chase phantoms while the real vessel conducts illegal activity.
9.2.3. The Iranian Innovation Leadership
Iran pioneered AIS manipulation as early as 2012.
IRGC-linked operators now use advanced GPS simulators and signal-hopping transmitters, enabling vessels to remain functionally untraceable for weeks.
9.3. “Dark Shipping” as a System: When Silence Becomes a Strategy
Turning off AIS is technically illegalو but widely practised.
9.3.1. Where Ships Go Dark
Common dark zones include:
- Gulf of Oman
- Hormuz Strait
- Malaysian coast (Tanjung Bruas & Sungai Udang)
- South China Sea
- Eastern Mediterranean
These regions offer “shadow corridors” where enforcement is weak.
9.3.2. Dark Shipping Patterns
When going dark, vessels typically:
- Slow down to minimum navigation speed
- Drift to meet another ship
- Conduct STS transfers
- Re-emerge near a legal port
This allows large quantities of sanctioned crude to be laundered into the legitimate supply chain.
9.4. Vessel Identity Laundering: How Ships Acquire New Lives
Shadow Fleet tankers often cycle through 3–7 identity changes in their lifetime.
9.4.1. The Three Pillars of Identity Laundering
- IMO Number Misuse
Still illegal, but increasingly common:
Some tankers alter digits on the hull and broadcast a stolen IMO registration. - Asset Re-flagging (Flag Hopping)
Ships may switch flags:
- Monthly
- Weekly
- Sometimes within 48 hours
Flags of convenience, such as Tanzania, Cameroon, and Gabon, provide instant registration with minimal vetting.
- Ship Renaming & Cosmetic Alterations
Crews repaint ships between voyages to avoid satellite-based visual confirmation.
9.5. Ownership Camouflage: Corporate Layers as Shielding Armour
Digital deception at sea is only half the story.
On land, the Shadow Fleet relies on opaque ownership cloaking, typically built through:
- Shell holding companies
- Nominee directors
- “Disappearing” corporate entities
- Offshore corporate registrar inconsistencies
9.5.1. High-Risk Registries
The Shadow Fleet heavily uses corporate registrations in:
- Marshall Islands
- Seychelles
- St. Kitts & Nevis
- Panama
- Hong Kong (front entities)
- Dubai free zones
These jurisdictions enable rapid corporate creation and dissolution, making asset tracing extremely difficult.
9.6. Cybersecurity & Data Manipulation: The New Phase of Evasion
In recent years, IRGC-linked operators and Russian shipping networks have begun deploying cyber-enabled evasive methods.
9.6.1. Data Pollution
Some tankers inject false metadata into:
- Lloyd’s List databases
- Port arrival registries
- Customs documentation
This creates contradictory records that hinder enforcement.
9.6.2. Credit Laundering Through Blockchain
Some sanctions-evading networks use:
- “Shadow invoices”
- Blockchain-based settlement
- Cryptocurrency-linked shipping brokers
These techniques allow payments to circumvent SWIFT controls.
9.7. The Technology Providers: Who Enables the Shadow Fleet?
This section identifies key enablers (without naming specific companies to maintain safety & academic compliance):
Categories of Enablers
- Transponder suppliers selling modifiable AIS units
- Navigation software vendors whose tools are exploited
- Satellite communication brokers offering encrypted channels
- Marine equipment traders in the UAE, Malaysia, and Hong Kong
- Intermediary shipping agencies providing falsified voyage plans
These technologies are often sold legally, but exploited for illegal use.
9.8. Counter-Tech: How Enforcement Agencies Fight Back
Despite the sophistication of deception, global enforcement is advancing.
9.8.1. Machine-Learning-Based Vessel Behaviour Analysis
Systems now track:
- Unnatural course deviations
- Repetitive dark patterns
- Suspicious loitering
- Identity inconsistencies
AI maritime surveillance has begun identifying “probable shadow fleet vessels” with 80–92% accuracy.
9.8.2. Satellite-Based Verification
Tools include:
- SAR imaging (detects metal objects even at night)
- Hyperspectral oil plume detection
- Satellite optical comparison with AIS signals
This is closing the gap between digital deception and physical reality.
9.8.3. Regulatory Advancements
The EU, OFAC, and IMO are expanding:
- AIS compliance standards
- Sanctions lists
- Port state control inspections
- Insurance vetting requirements
The Shadow Fleet is entering a more hostile environment — though far from defeated.
Chapter 10 — Future Outlook: Will the Shadow Fleet Survive Increasing Global Enforcement?
The Shadow Fleet has thrived for over a decade by exploiting regulatory blind spots, fragmented maritime governance, and the global hunger for cheap oil. But the question now looming over policymakers, insurers, and energy markets is clear: How long can this opaque, sanctions-evading fleet continue to operate before the walls close in?
This chapter examines the future trajectory of the Shadow Fleet in light of tightening global enforcement, the evolving technological landscape, rising insurance risks, and geopolitical shifts. It also evaluates potential disruptions—including stricter IMO rules, coordinated sanctions, digital monitoring systems, and legal liabilities for ship owners and ports that knowingly facilitate illicit trade.
10.1: Increasing Global Pressure: A New Enforcement Era
After years of fragmented enforcement, the maritime world is shifting toward collective pressure. Multiple forces are converging:
- Sanctions Coalitions Are Becoming More Unified
- The U.S., EU, UK, Japan, and Australia have begun synchronising maritime sanctions lists.
- Shared intelligence between navies and financial regulators is closing long-standing loopholes.
- Analytical platforms such as Lloyd’s List Intelligence and Windward AI provide international partners with near-real-time vessel risk scores.
- Stricter Insurance Regulations
- Western insurers now require verified AIS data, independent inspections, and vessel age compliance before issuing coverage.
- This limits the ability of old, risky tankers to operate undetected.
- IMO Digitalisation Reforms
By 2026, IMO aims to make digital reporting, enhanced ship identification, and standardised AIS auditing mandatory—reducing the feasibility of spoofing, identity swapping, or going dark.
- Naval Monitoring of Hotspots
Key chokepoints like the Strait of Hormuz, South China Sea, and Mediterranean now have joint naval surveillance programs using satellite imaging, drones, and synthetic-aperture radar (SAR).
Outcome: It is becoming far harder for Shadow Fleet vessels to disappear—or lie—without detection.
10.2: Will the Shadow Fleet Adapt or Collapse?
The Shadow Fleet is resilient because it constantly evolves. However, each tactic it relies on is becoming more costly or risky.
Adaptation Scenario (Survival):
- Expanded use of flags of convenience from states willing to ignore sanctions.
- Creation of even more layered shell companies through offshore jurisdictions.
- Technological upgrades to spoof AIS more convincingly.
- Greater reliance on Russian, Chinese, and Venezuelan ports that do not enforce Western sanctions.
Collapse Scenario (Decline):
- Rising insurance losses due to ageing tankers cause global insurers to blacklist entire corporate groups.
- Ports begin rejecting undocumented or high-risk tankers to avoid legal consequences.
- Coordinated sanctions start identifying beneficial owners, not just the vessels.
- Increasing global monitoring makes deceptive manoeuvres statistically impossible to hide.
The most realistic outcome is partial survival: the fleet will shrink but not disappear.
10.3: Economic and Legal Risks That Could End the Shadow Fleet
Ageing Tankers = Soaring Risk
Over half of the Shadow Fleet’s VLCCs and Suezmax vessels are 20–26 years old, beyond the normal commercial lifespan. Mechanical failures, oil spills, and environmental disasters are becoming more likely.
A single catastrophic spill could trigger:
- International lawsuits
- Port bans
- Criminal prosecutions
- Heavy marine insurance crackdowns
Expanding Legal Accountability
Future enforcement will focus on:
- Beneficial ownership tracing
- Criminal liability for corporate officers
- Port State fines
- Seizures through civil asset forfeiture
The Shadow Fleet thrives on anonymity—but that anonymity is eroding.
10.4: Technological Disruption: The End of “Dark Shipping”?
Major advancements threaten the fleet’s ability to operate covertly:
Multi-source AIS Verification
Combining terrestrial AIS, satellite AIS, SAR imaging, and optical imagery will detect even “dark” vessels.
Machine-Learning Pattern Detection
Algorithms can now identify:
- STS transfer hotspots
- Suspicious loitering patterns
- Identity anomalies
- Flag-hopping cycles
- Vessels washing AIS tracks
Global Maritime Blockchain Systems (Under Development)
Several nations are testing blockchain-based vessel identity systems that would eliminate spoofing.
Once these technologies become mandatory, dark shipping will become statistically impossible.
10.5: Geopolitical Variables That May Prolong the Shadow Fleet
Despite enforcement tightening, several geopolitical factors may extend the lifespan of the fleet:
- High global oil prices incentivise buyers to seek discounted Iranian/Russian crude.
- Weak or corrupt maritime jurisdictions continue to issue flags with zero oversight.
- China and India—major buyers of sanctioned oil—may choose not to join Western enforcement efforts.
- Proxy ownership networks will continue exploiting legal gaps between jurisdictions.
Thus, geopolitics—not technology—may ultimately determine whether the fleet endures.
10.6: Outlook — The Beginning of the End
The Shadow Fleet will not disappear overnight. But the convergence of legal, technological, and regulatory changes suggests a clear trajectory:
- 2025–2027: Shrinkage of high-risk vessels as insurance and port restrictions tighten.
- 2027–2030: Widespread adoption of AI maritime monitoring systems makes AIS deception nearly impossible.
- 2030+: Shadow Fleet becomes smaller, more fragmented, and less profitable—relying on only the most corrupt or opaque jurisdictions.
The era of anonymous tankers roaming international waters with impunity is closing—and the Shadow Fleet will likely face its greatest pressure in the next five years.
Conclusion
The global “Shadow Fleet” is no longer a mysterious set of rogue tankers—it is a fully engineered sanctions-evasion architecture, built deliberately by states like the Islamic Republic of Iran and supported by a parallel ecosystem of brokers, shell companies, ship managers, insurers, and complicit flag registries. What began as a workaround has evolved into a sophisticated maritime economy designed to inject sanctioned oil into global markets while bypassing international oversight.
Throughout this investigation, the evidence reveals a disturbing truth:
This fleet is not simply exploiting loopholes—it’s exploiting the weaknesses of international maritime governance itself.
AIS spoofing, identity laundering, STS operations, and multi-layered corporate concealment are not isolated tactics; they are components of a coordinated strategy that undermines sanctions frameworks, distorts global energy pricing, and finances destabilising activities across the Middle East and beyond.
Yet the system is not unbreakable.
As regulators, satellite-tracking experts, insurers, and classification societies sharpen their detection methods, the Shadow Fleet faces growing pressure. The future of sanctions enforcement will depend on real-time transparency, cross-border data cooperation, and a zero-tolerance approach to flags of convenience and ownership opacity.
Ultimately, the Shadow Fleet is a symptom, not a cause. As long as authoritarian regimes depend on covert oil sales for survival—and as long as the maritime system rewards secrecy—this global network will mutate and adapt. What the world decides to do next will determine whether the Shadow Fleet remains an anomaly
—or becomes the new normal in international shipping.